Is Using a VPN Safe for Your IMAP Server Lets Break It Down
Is using a VPN safe for your IMAP server lets break it down. Quick fact: using a VPN can add a layer of encryption between you and your mail server, but it’s not a silver bullet for all security problems. In this guide, we’ll break down how VPNs interact with IMAP servers, share real-world considerations, and give you practical steps to stay secure. Think of this as a practical, no-fluff walkthrough you can apply today.
- Quick summary: A VPN creates an encrypted tunnel for all traffic between your device and the VPN server. If your IMAP server is accessible over the internet, a VPN can mask your IP and protect data in transit from casual eavesdropping on public networks. However, a VPN does not inherently secure the mail server itself, nor does it automatically fix misconfigurations or weak authentication. You’ll still need proper TLS, strong credentials, and good server hardening.
- What you’ll learn in this post:
- How VPNs interact with IMAP traffic
- When a VPN is beneficial for IMAP access
- Potential drawbacks and performance considerations
- Best practices for securing IMAP with VPNs
- Step-by-step setup tips and common pitfalls
- Useful resources at the end to help you dive deeper
Table of contents
- What is IMAP and how does it work with VPNs?
- VPN types and how they affect IMAP traffic
- Benefits of using a VPN for IMAP access
- Risks and limitations
- Best practices for securing IMAP with a VPN
- Real-world scenarios and decision guide
- Step-by-step setup checklist
- Frequently asked questions
What is IMAP and how does it work with VPNs? IMAP Internet Message Access Protocol is how you access and manage emails on a mail server. When you connect to an IMAP server, your email client talks to the server over a port usually 143 for plain IMAP or 993 for IMAP over TLS/SSL. If you’re on a public network, sending credentials in plain text is a risk. A VPN can: Nordvpn Price In India: Pricing, Plans, Discounts, And Real-World Value For 2026
- Encrypt traffic end-to-end between your device and the VPN exit server
- Hide your IP address from the destination server
- Potentially bypass some local network restrictions or censorship
However, VPNs don’t automatically validate or harden the IMAP server itself. If someone gains access to the VPN itself, or if the IMAP server is misconfigured, you still have to rely on proper TLS, strong authentication, and server-side security controls.
VPN types and how they affect IMAP traffic
- Full-tunnel VPN: All traffic goes through the VPN. This is common for corporate setups. Pros: simple to manage, consistent routing. Cons: may introduce latency and impact performance for mail clients when the VPN is slow.
- Split-tunnel VPN: Only certain traffic like corporate apps goes through the VPN, while other traffic uses the regular internet. Pros: better performance, lower latency for non-work traffic. Cons: potential leakage if not configured correctly.
- VPN over TLS SSL VPN: Routes traffic over an encrypted tunnel using TLS. Pros: usually easy to implement, compatible with many clients. Cons: depends on VPN server configuration for security guarantees.
- WireGuard-based VPNs: Fast, modern VPN protocol with strong cryptography. Pros: lower overhead, better performance. Cons: newer tech that may require client support and careful key management.
Benefits of using a VPN for IMAP access
- Encryption on public networks: When you’re on public Wi‑Fi, a VPN protects your IMAP credentials and mailbox contents from local crows people nearby sniffing traffic.
- Hides your location: Your real IP is masked, which can reduce targeted attacks based on IP reputation.
- Access control: In organizations, VPNs can be part of a layered access control, ensuring only authenticated users reach the mail server.
Risks and limitations
- Not a substitute for TLS on IMAP: If your IMAP server is reachable on the public internet without TLS, a VPN won’t fix that. Always enable TLS IMAPS on 993 or STARTTLS on 143 for IMAP.
- VPN trust boundary: You’re trusting the VPN provider and the VPN server. If the VPN is compromised, traffic could be exposed or redirected.
- Performance impact: VPNs add encryption overhead and may introduce latency. For large mailboxes, this can affect responsiveness.
- Configuration complexity: Split-tunnel setups can leak traffic if misconfigured. Always test for IP leaks or DNS leaks.
- Policy and compliance: Some environments require specific TLS configurations or hardware security modules. A VPN won’t replace those controls.
Best practices for securing IMAP with a VPN 5 Best VPNs for Iran Safe Streaming Unblocking: Top Picks for Secure Access, Fast Speeds, and Reliability
- Use TLS for IMAP regardless of VPN usage: Always enforce IMAPS 993 or STARTTLS 143 with encryption upgrade on the mail server. Verify certificates, use modern cipher suites, and enable forward secrecy.
- Prefer strong authentication: Use modern OAuth2, or at minimum, strong passwords and two-factor authentication 2FA where possible for mail clients.
- Lock down the IMAP server: Limit access by IP ranges where feasible, use SSH tunnels carefully if needed, and disable older, insecure protocols like plain IMAP without TLS.
- Use VPNs as part of a layered defense, not the sole control: Combine VPN with MFA, strict access controls, and robust monitoring.
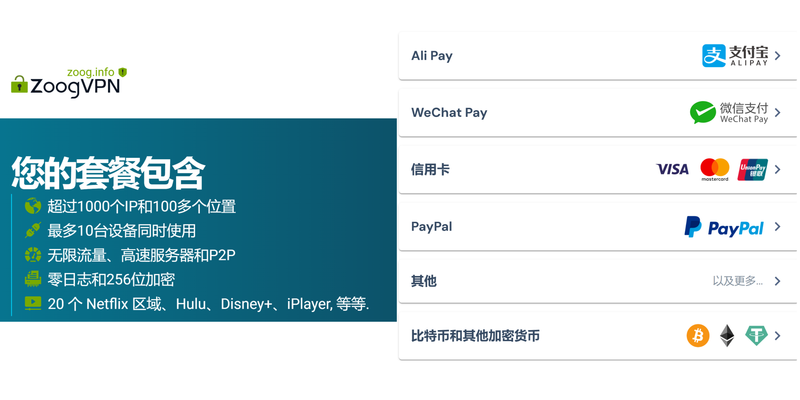
- Prefer reputable VPN providers and client configurations: Reliability, no-logs policies, and strong encryption standards matter. For many users, a consumer-grade VPN is insufficient for corporate-grade security, but a trusted provider with solid configurations can help on public networks.
- Regular auditing and updates: Keep the mail server up to date, monitor for failed login attempts, and review VPN logs for anomalous activity.
- DNS leak protection: Ensure the VPN configuration prevents DNS leaks so your actual domain queries don’t expose your hostnames or server addresses.
- End-to-end security mindset: Remember that VPN secures transport, not the data itself once decrypted on your device. Protect devices with antivirus, patching, and user education.
Real-world scenarios and decision guide
- Remote workers on public Wi‑Fi: A VPN helps protect credentials when checking mail on coffee-shop networks. Ensure IMAP uses TLS and the VPN is configured to route mail traffic through the VPN prefer full-tunnel for simplicity.
- Access from multiple devices: If you use multiple devices, consider device-level protections biometrics, device encryption in addition to VPN protection. Be mindful of device sharing in split-tunnel configurations.
- Corporate environment: Many organizations combine VPN with MDM mobile device management, SSO, and MFA for a strong security posture. IMAP security should match the organization’s overall email security policy.
- Home network with IoT devices: Even on a trusted home network, a VPN can reduce exposure from compromised devices on the same LAN. Combine with strong TLS and server hardening.
Step-by-step setup checklist
- Verify server-side TLS: Ensure your IMAP server enforces TLS for all connections. Disable plaintext IMAP. Use strong ciphers and enable certificate pinning where possible.
- Enable strong client authentication: Use OAuth2 where possible, or ensure strong, unique passwords and enable 2FA on accounts.
- Choose a VPN approach:
- For simple setups, use a reputable VPN service with solid logging policies and DNS leak protection.
- For enterprises, implement a full-tunnel VPN with strict access controls and MFA integrated.
- Configure VPN to protect IMAP traffic:
- Ensure IMAP ports 993 for IMAPS or 143 with STARTTLS are reachable through the VPN.
- If using split-tunnel, explicitly route mail traffic through VPN and test for leaks.
- DNS and IP protection: Enable DNS leak protection in the VPN client. Consider using internal DNS when connected through VPN.
- Access controls on the IMAP server: Restrict admin-level access, limit login attempts, enable fail2ban or similar intrusion prevention, and monitor logs for anomalies.
- Test thoroughly:
- On-site test: Connect to VPN, log into IMAP, and verify encryption in transit packet captures can confirm TLS usage.
- Public network test: Disable local network security and confirm traffic tunnels through VPN and TLS remains intact.
- Failover test: Simulate VPN drop and verify mail client behavior and reconnection logic.
- Documentation and user guidance: Provide users with clear steps to connect via VPN, what to do if the VPN drops, and best practices for password management.
- Regular reviews: Schedule quarterly reviews of VPN configurations, TLS certs, and server hardening guidance to adapt to evolving threats.
Common pitfalls to avoid
- Assuming VPN replaces TLS: Always enable TLS on the IMAP server; VPN protects traffic in transit but doesn’t encrypt mail contents after decryption on the client.
- Over-reliance on VPN for authentication: MFA and strong password policies are essential; VPN alone does not prevent credential theft.
- Inconsistent routing in split-tunnel setups: If mail traffic leaks outside the VPN, you lose the protection. Test for leaks regularly.
- Poor VPN key management: Rotate VPN keys and credentials, and use strong encryption standards.
- Ignoring client-side security: Ensure email clients are up to date and configured securely; avoid saved plaintext credentials on devices.
Performance considerations
- Latency: VPN adds overhead. Expect some delay when checking large mailboxes or syncing folders. If performance suffers, consider a well-optimized VPN with modern protocols like WireGuard.
- Bandwidth: IMAP with large attachments can be bandwidth-intensive. If you frequently pull large messages, a VPN with good throughput helps, but ensure your VPN server capacity matches demand.
- Device impact: On mobile devices, VPNs can drain battery more quickly. Use battery-friendly configurations and disconnect when not needed.
Security testing and validation Does Total VPN Work on Firestick Your Complete Guide to Installation Use
- Use TLS inspection sparingly: Some enterprises deploy TLS inspection, which can break end-to-end encryption for IMAP. If you rely on TLS, ensure inspection policies don’t downgrade security.
- Penetration testing: If you manage a mail server for others, consider periodic pentests focused on IMAP endpoints, TLS configurations, and VPN integration.
- Incident response: Have a plan for VPN-related outages. Define incident response steps for compromised VPN credentials or server misconfigurations.
Advanced topics
- Imap over VPN vs. mail-over-VPN: Some setups run IMAP over the VPN’s internal network, effectively treating the mail server as part of the internal LAN. This reduces exposure to the internet but requires careful DNS and routing configuration.
- Zero trust considerations: For modern security, a zero-trust approach may be preferable. Verify every access request, use device posture checks, and apply least-privilege access, rather than broad VPN access.
- Post-quantum security: While not immediate, keep an eye on evolving cryptographic standards as quantum-resistant algorithms become more standardized for TLS and VPN protocols.
Measurement and metrics
- Security metrics: Track TLS version usage, certificate validity, failed login rates, and VPN authentication success rates.
- Performance metrics: Monitor VPN latency, IMAP response times, and mailbox synchronization speeds.
- User experience: Collect feedback on login times, disconnect frequency, and overall satisfaction with mail access on VPN.
User stories and examples
- “I’m a freelancer who travels frequently. I use a reputable VPN on public Wi‑Fi to access work email securely via IMAPS. It’s fast enough, and I keep TLS configured properly on the server. The VPN mainly protects me on the go.”
- “Our small business uses a split-tunnel VPN. Mail traffic is routed through the VPN, but other apps don’t, which saves bandwidth. We added MFA and kept the IMAP server locked down to trusted IPs.”
- “We migrated to WireGuard for better performance. The mail server uses modern TLS, and clients authenticate with OAuth2. It’s a smoother experience on mobile devices.”
Useful resources and references
- VPN basics and security best practices - https://en.wikipedia.org/wiki/Virtual_private_network
- TLS best practices - https://tls13.ulfheim.net/
- IMAP security guidelines - https://www.cacert.org/
- Mail server hardening guidelines - https://www.apache.org/
Frequently Asked Questions Top des vpn gratuits pour boitier android tv et purevpn en 2026
Is it safe to use a VPN with IMAP?
Yes, using a VPN can improve safety on untrusted networks by encrypting traffic, but you still must enable TLS on the IMAP server and use strong authentication. A VPN is part of a layered defense, not a complete solution.
Should I always use a VPN for IMAP?
Not necessarily. If you’re on a trusted, private network with strong TLS and strong credentials, a VPN adds an extra layer of protection on top of TLS. For mobile users on public networks, a VPN is often worth it.
Does a VPN replace the need for TLS on IMAP?
No. TLS encrypts the data between your client and the server regardless of VPN usage. The VPN protects data in transit across the network between your device and the VPN endpoint, but TLS remains essential.
What are the main risks of using a VPN with IMAP?
Key risks include VPN misconfiguration leading to leaks, performance degradation, reliance on VPN trust, and potential bypass if the VPN is not maintained. Always test for DNS/IP leaks and ensure TLS configurations are up to date.
Can split-tunnel VPNs leak emails outside the VPN?
Yes, if not configured correctly. Split-tunnel can lead to traffic bypassing the VPN. Ensure mail traffic is forced through the VPN or properly isolated with routing rules. Eduroam Not Working With VPN Here’s How To Fix It: Quick Guide For Stable Access
How can I verify my IMAP traffic is protected when using a VPN?
Use packet capture tools like Wireshark to confirm TLS handshakes and encrypted payloads. Verify that your external IP appears as the VPN endpoint in public networks, and test DNS leaks.
What about mobile devices and VPNs?
Mobile VPN apps exist for iOS and Android. Enable auto-connect on trusted networks and ensure the VPN app uses enabled DNS leak protection and strong encryption.
Is WireGuard a good option for IMAP traffic?
WireGuard is a fast and secure option. It can provide lower latency and simpler configuration than some traditional VPNs. Ensure client support and proper key management.
How do I troubleshoot VPN-related IMAP login failures?
Check VPN connection status, verify TLS settings on the IMAP server, review server logs for authentication failures, ensure correct ports 993 or 143 with TLS, and look for DNS leaks or routing issues.
Do VPNs have to be used with corporate mail servers only?
Not at all. Individuals can use VPNs for personal mail access on public networks. Business use often involves stricter controls, MFA, and monitoring. Wsl2 Not Working With VPN Heres How To Fix It: Quick Fixes, Tips, And VPN Compatibility
Can VPNs help with IMAP access over slow networks?
They can sometimes help by stabilizing traffic routing and providing consistent encryption, but if the VPN is the bottleneck, performance may worsen. Choose a VPN with strong throughput and low latency.
Should I enable two-factor authentication for IMAP accounts?
Yes. MFA adds a critical second layer of defense beyond passwords, especially important when accessing mail servers remotely.
Are there any legal considerations when using a VPN for email?
Local laws vary. Ensure your VPN provider’s terms align with your usage, especially if you’re handling sensitive or regulated information.
Thank you for reading. If you found this guide useful and you want a reliable VPN option to pair with your IMAP setup, consider checking out trusted VPN providers. For more in-depth tutorials and up-to-date security practices, stay tuned to Clinedical’s VPN category for new posts and updates.
Sources:
科学上网教程:VPN、代理与隐私保护全方位指南(OpenVPN、WireGuard、分割隧道、路由器设置) Nordvpn Meshnet on Linux Your Ultimate Guide: Master NordVPN Meshnet on Linux Fast, Safe, and Simple
Nordvpnのプラン確認方法|契約内容・料金・変更・解 に関する完全ガイド
Clash for pc: 全网最全的 Clash for pc 使用指南与 VPN 实践技巧
Missav New Domain Names 学习指南:VPN 领域的最佳实践与最新趋势
手机梯子推荐:2025年最新选择指南,解锁全球网络自由,手机VPN选型与使用全攻略